In a previous post, I explained the steps to take to create a Windows Active Directory (AD) and get it ready for client computers to join. You can find the post here. Today, I will be walking through the process of joining a Windows 10 client to the AD and also some “fun” things we can do with the AD, and try to replicate some domain/enterprise-wide settings used in the real world.
I previously downloaded the Windows 10 Enterprise ISO from Microsoft’s Evaluation Centre, but I recently found out that Microsoft no longer supports it, and it can’t be found on the website anymore. I have uploaded the same ISO that I used to run this lab here.
1. Setting up Windows Client
I normally would run this lab on VirtualBox, but I clumsily spilled margaritas on my Intel MacBook, and my new Apple Silicon MacBook doesn’t work well with VirtualBox. So, for this lab, I used UTM. Took some getting used to, but I figured it out. I have also linked how I ran this lab on VirtualBox on my GitHub here.
Here’s what I did:
-
New Virtual Machine > Emulate >
Windows>x86_64 -
CPU Cores: 4
-
Memory: 8 GB (I have 32 GB total on my Mac)
-
Boot Firmware: UEFI
-
Storage: 100 GB
-
Network:
Emulated VLAN
Attached the Windows 10 ARM ISO, then hit Create.
2. Installing Windows 10
Start the VM, it might be a little slower because we are using “Emulate” inside UTM and it is a different architecture than the ARM that the Mac runs on.
I went through these steps:
Select language and region.
Click Install Now.
Accept the license terms.
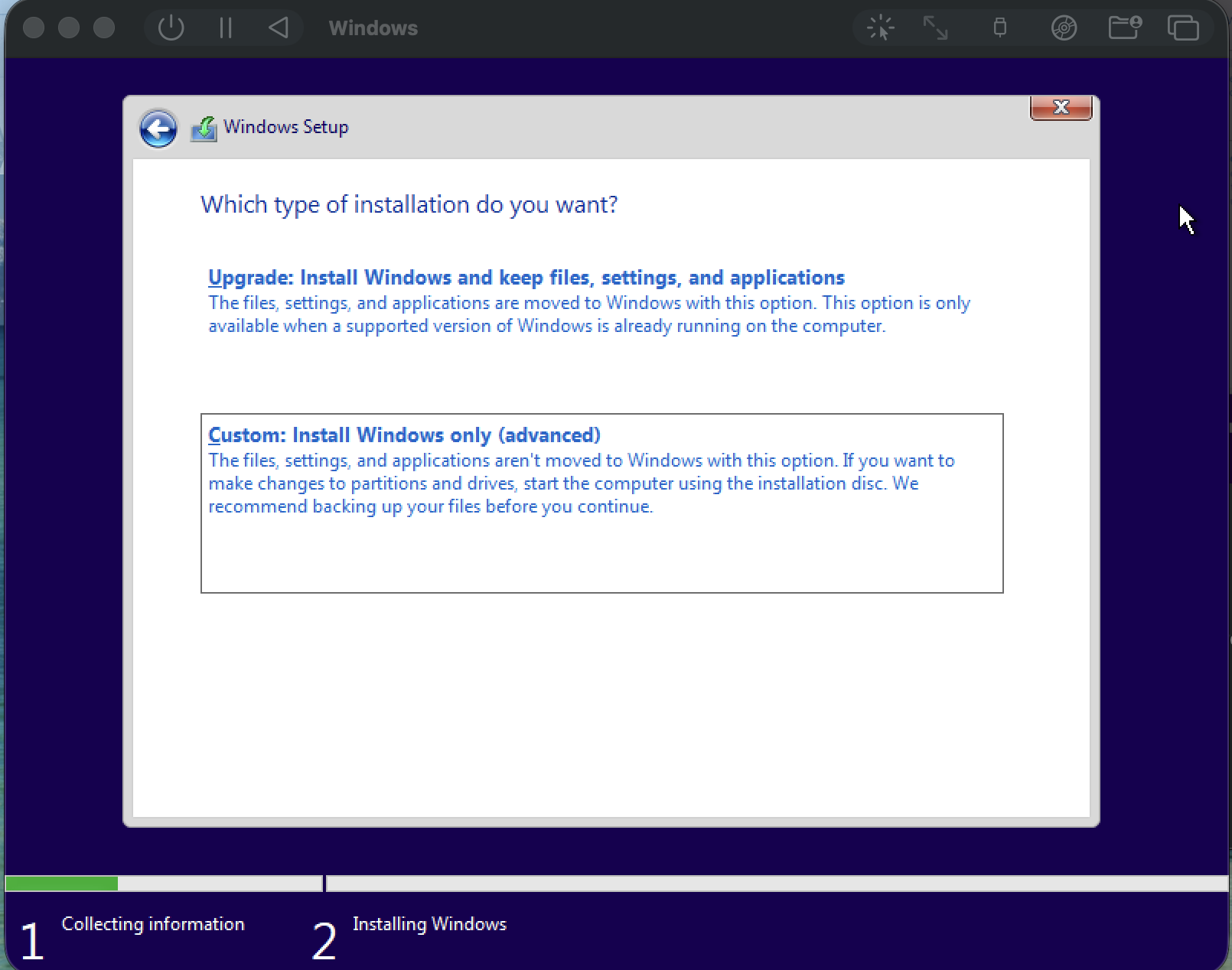
Choose “Custom: Install Windows only (advanced)”.
Create a new partition > Apply > Next.
Create a new partition, click Apply, then click Next to begin the installation.
The setup might take a while, and Windows will restart several times, just be patient, everything will work out. Don’t press any key.
Once complete, go through the initial setup: choose region, language, and keyboard layout.
I skipped setting a password since this client will eventually join a Domain Controller (DC).
3. Network Configuration
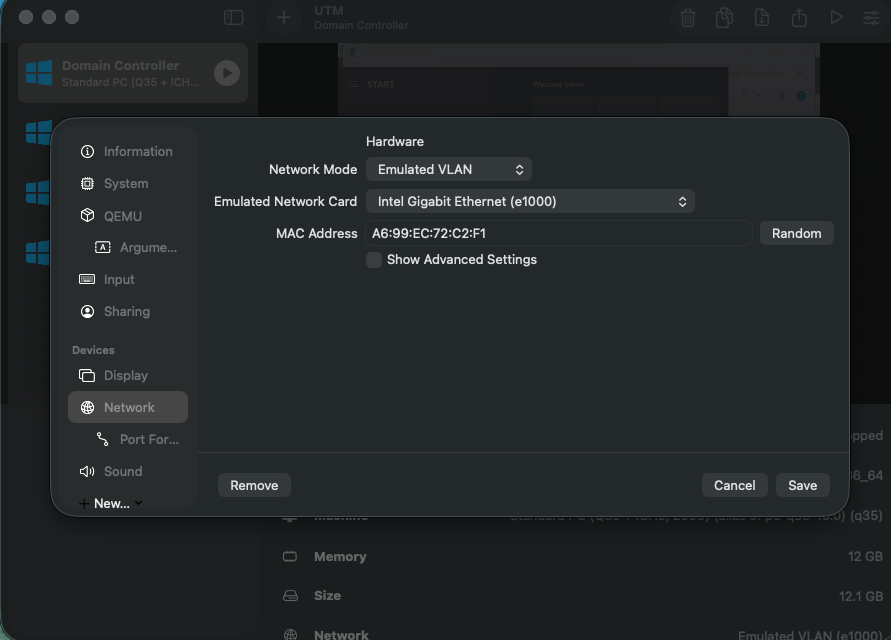
After installation, I shut down both the DC and the client to verify the network configuration. In UTM, I changed both network adapters from Shared to Emulated VLAN.
That isolates them from the host’s WiFi while still letting them talk to each other. The equivalent of this in VirtualBox is Internal Network.
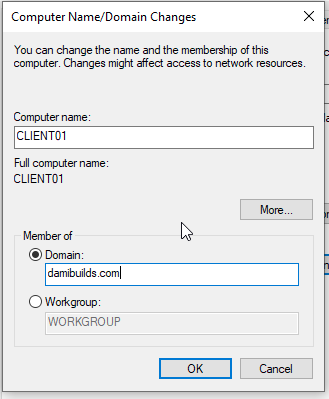
Then I renamed my Windows 10 client to CLIENT01 and rebooted it.
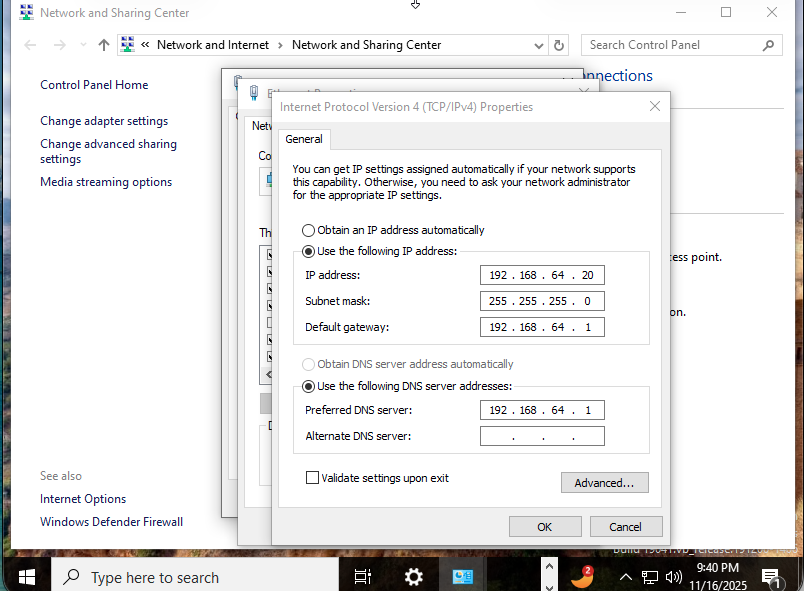
To make sure both machines can find each other consistently, I gave them static IP addresses:
DC: 192.168.64.10
Client: 192.168.64.20
Subnet: 255.255.255.0
Gateway: 192.168.64.1
DNS: 192.168.64.10 (the DC’s IP)
This part matters because if DNS points to anything else, the domain join will fail.
On the client:
Settings > Network & Internet > Ethernet > Change adapter options > Right-click Ethernet > Properties > IPv4 > Use the following IP.
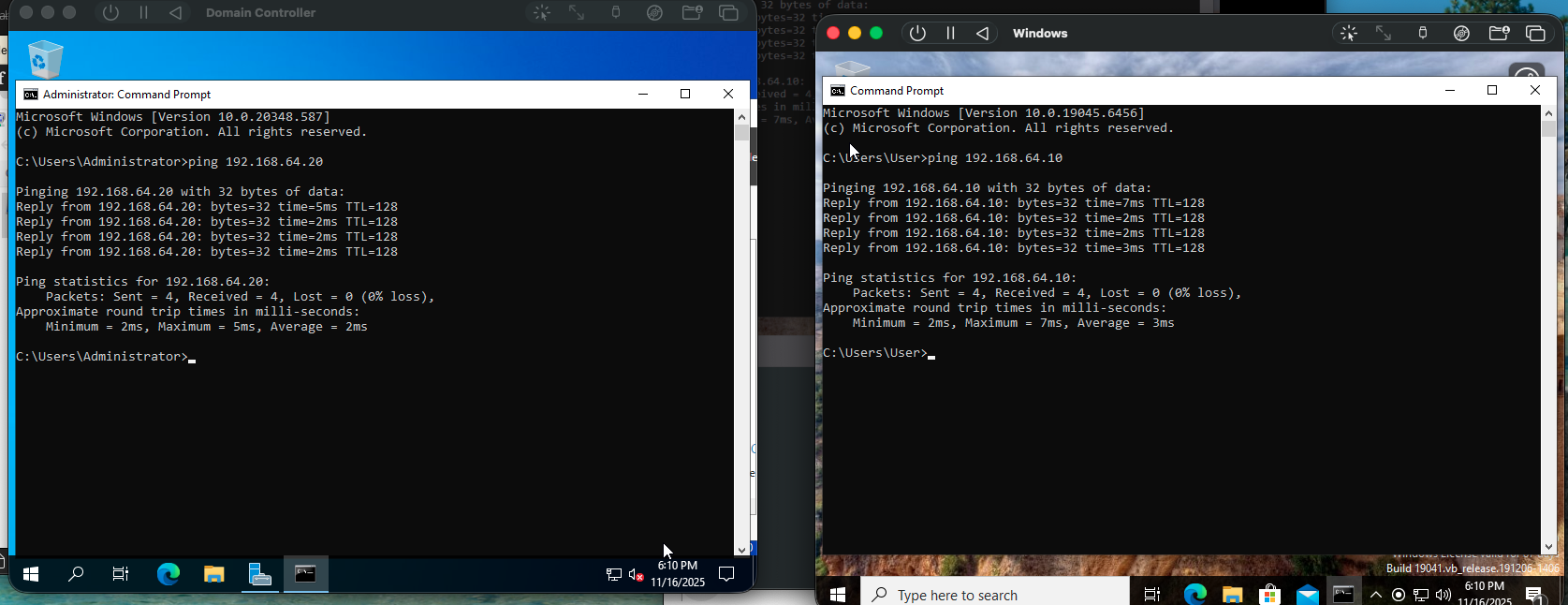
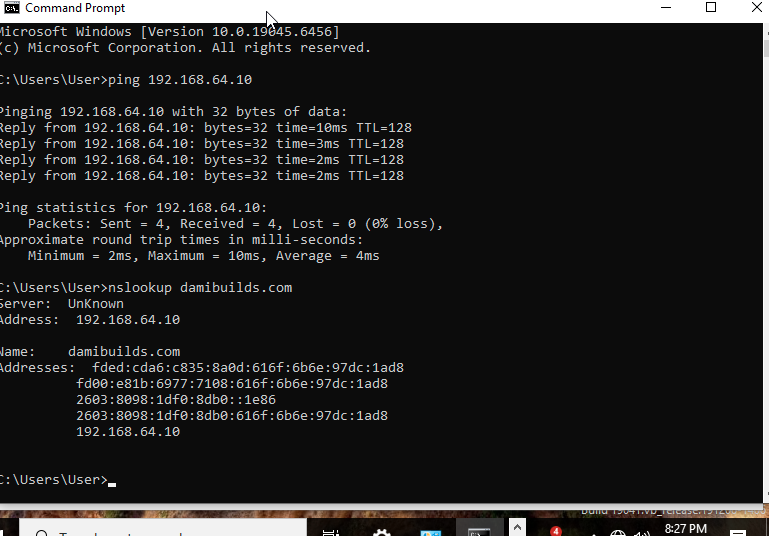
4. Testing Connectivity
After completing this, try pinging the DC’s IP from the client. Open CMD and run ping 192.168.64.10. If it doesn’t work, it’s almost always the network settings in UTM.
To fix it:
Shut down both VMs.
Go to Settings > Network on each.
Change the adapter to Bridged (Advanced) and select the same adapter (usually en0).
Save and reboot both systems.
Bridged mode lets the VMs talk to each other, the host, and the internet.
Once they’re up, ping the DC again from the client, it should now respond. If you try pinging the client from the DC and get “Destination Host Unreachable”, the client’s firewall is blocking it.
Quick fix: disable Windows Firewall on the client (not ideal, but acceptable for this lab). The proper fix in production would be to allow inbound ICMPv4 Echo Requests and Remote Service Management.
After that, both machines should ping successfully.
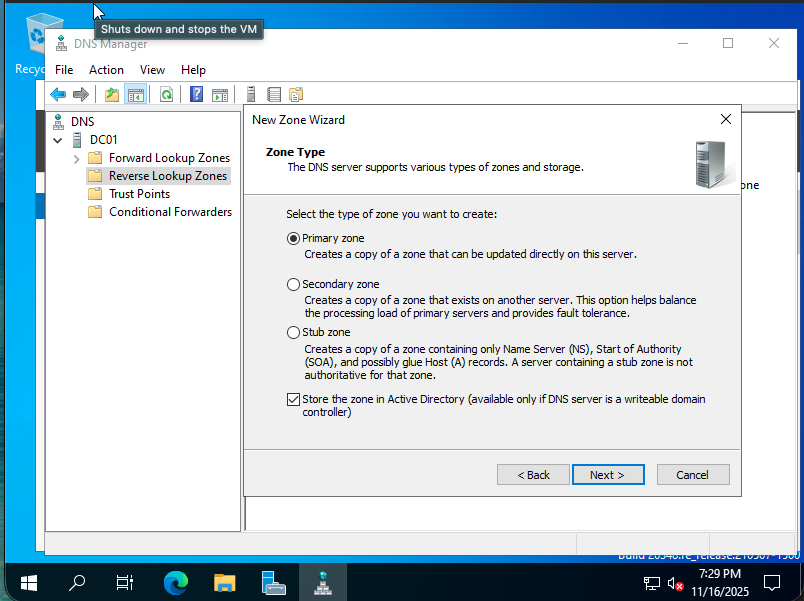
5. Setting Up DNS
On the DC, I opened DNS Manager > Right-click Reverse Lookup Zones > New Zone > Primary Zone > entered 192.168.64.
This makes name resolution cleaner and helps with AD diagnostics later.
6. Create Organization Units and Users
Inside Active Directory Users and Computers (ADUC):
Created three new OUs: Users, Computers, and Service Accounts.
Then made a test account under Users:
Name: Lab User
Username: labuser
Password: Password123@!
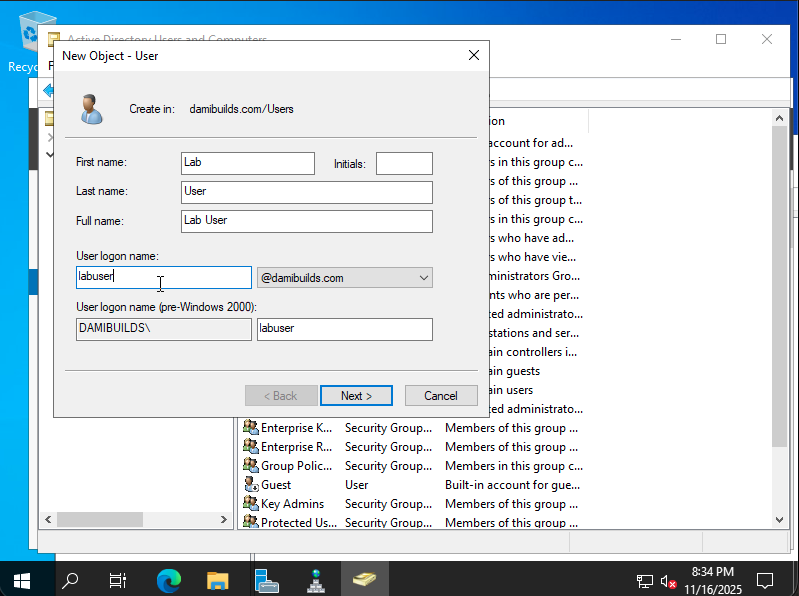
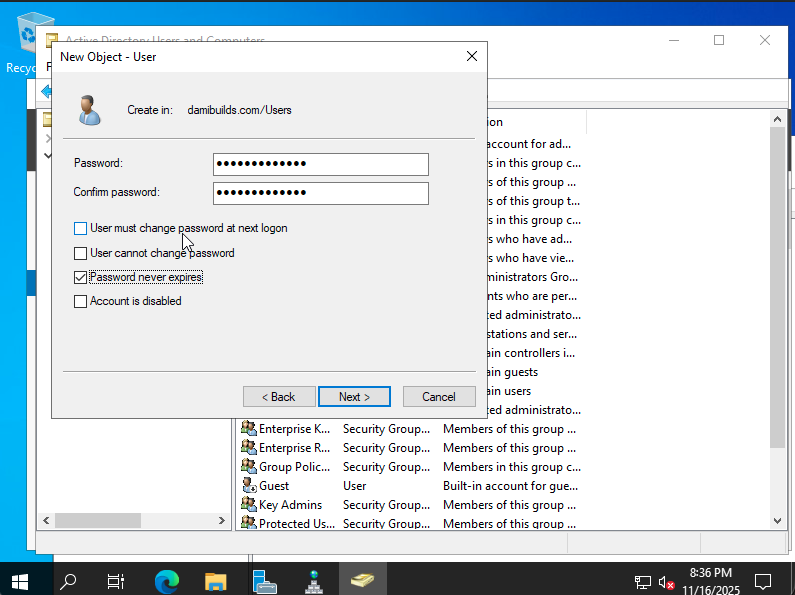
I didn’t check “User must change password at next logon” since this is a lab and not a compliance audit.
7. Verifying DNS Isolation
I was about to begin the process of joining, so I ran nslookup damibuilds.com, and it resolved to the actual IP of damibuilds.com, meaning my client had internet access and the labs were not isolated.
I needed it to resolve to the IP of the DC, so I shutdown both VMs and changed the network setting to “Host Only” on both. Now, nslookup resolves to the IP of my DC. This means we are ready to join the client to the DC as they can clearly see each other.
8. Joining the domain
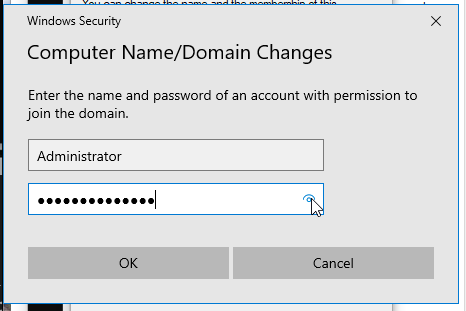
Back on the client, I opened:
Run -> sysdm.cpl -> Computer Name -> Change > Domain
Entered damibuilds.com, clicked OK, and got prompted for credentials.
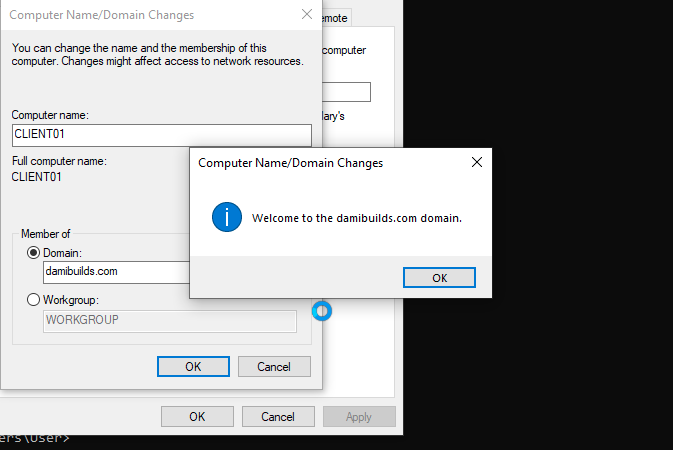
Used Administrator@damibuilds.com, hit enter, waited a few seconds…
“Welcome to the damibuilds.com domain.”
Best line of the entire lab.
Then it asked to restart, which I gladly did.
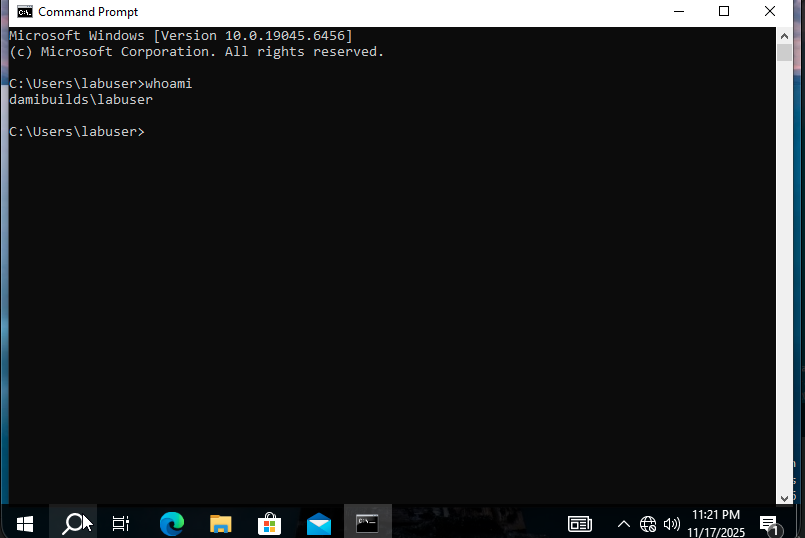
9. Verifying Join
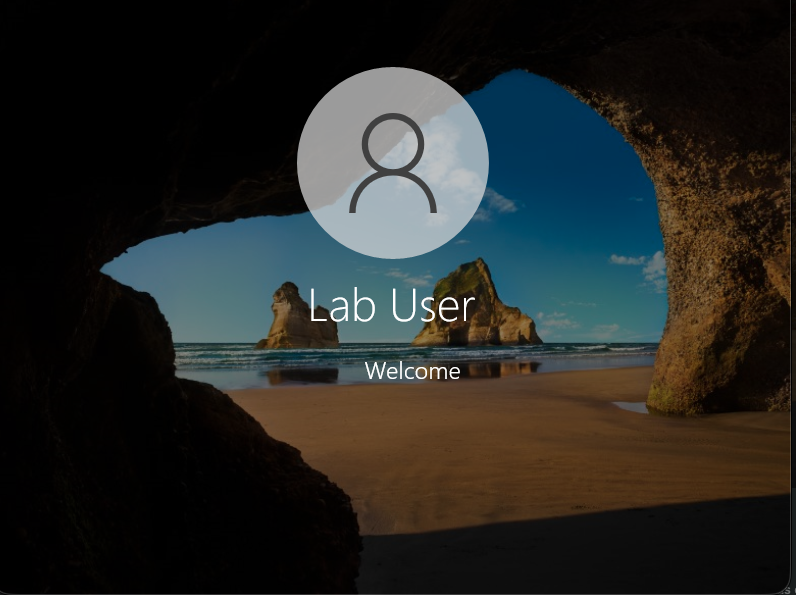
At the login screen, I clicked Other User and logged in as damibuilds\labuser.
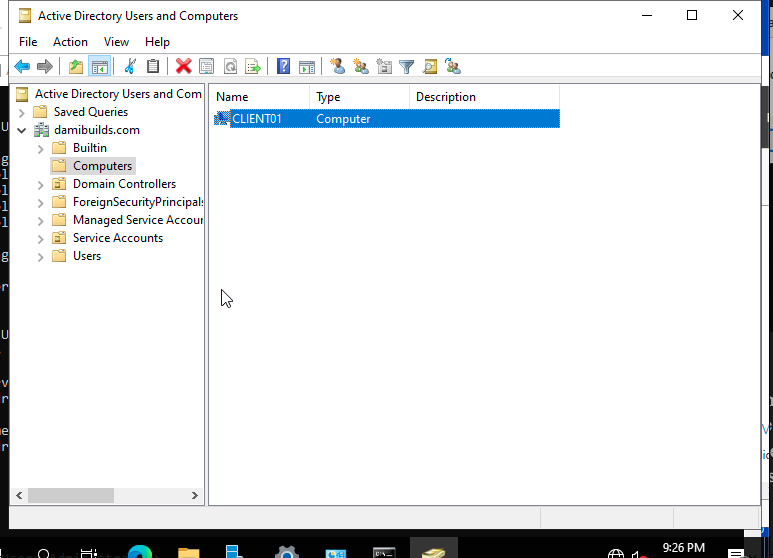
Back on the DC, I opened ADUC > Computers and saw CLIENT01 listed there.
That’s when you know everything’s wired up correctly.
Just for extra confirmation, I ran:
whoami
and got damibuilds\labuser.
All green.
Now lets explore what makes Active Directory such a core part of enterprise infrastructure.
10. Verifying Administrative Tasks
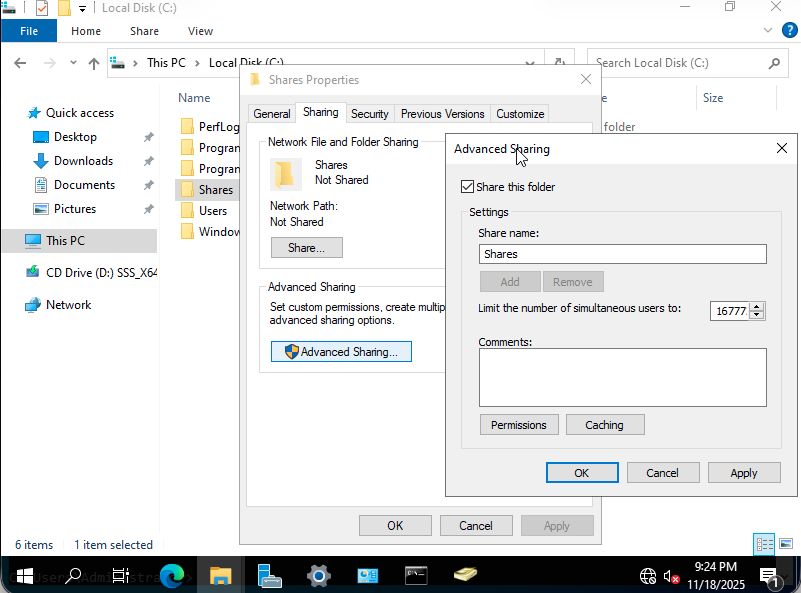
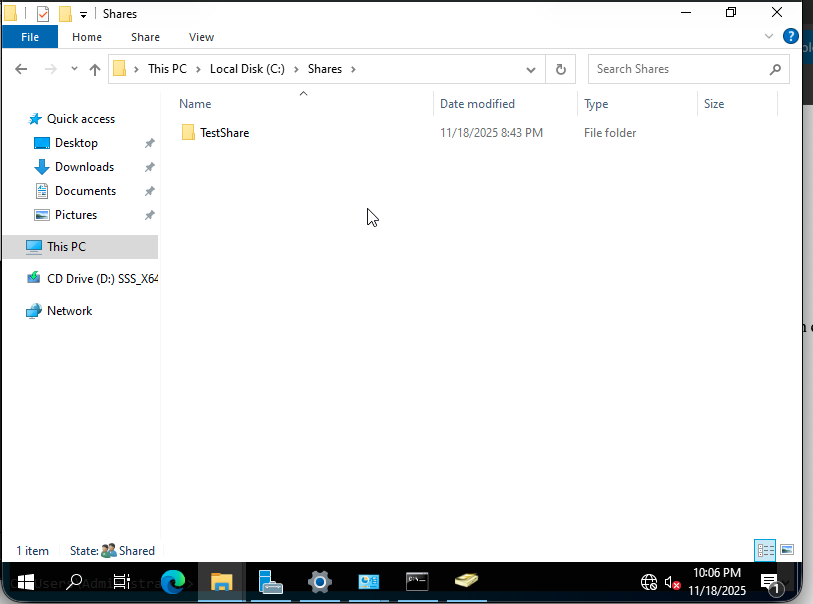
Create the Shared Folder
On the DC, navigate to C:\ and create a new folder called Shares\TestShare.
Right-click the folder > Properties > Sharing tab > Advanced Sharing > check Share this folder.
Click OK.
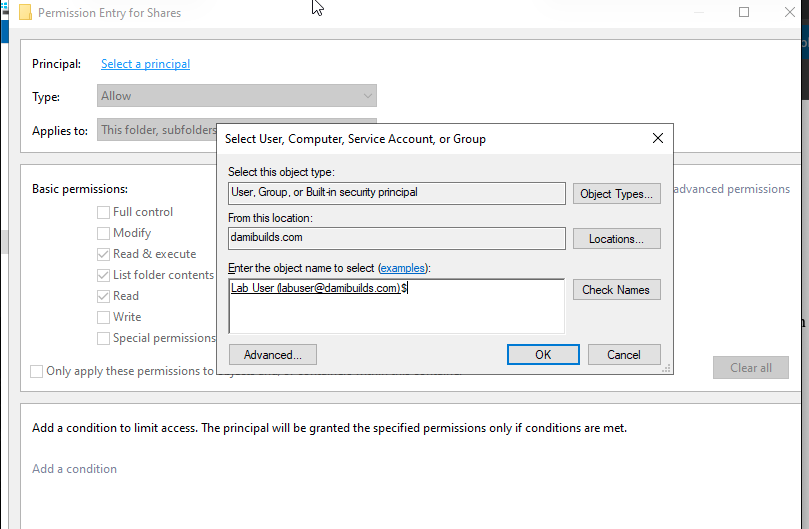
Set Folder Permissions
Right-click the shared folder again > Properties > Security tab > Advanced > Add.
Click Select a principal.
In the Select User or Group window, type damibuilds\labuser and click Check Names.
If it underlines, it means the user was found in Active Directory.
If it doesn’t, check that the client has joined the domain and that its DNS points to the DC.
Click OK, then assign the desired permissions for the user (Read, Modify, or Full Control).
Then click OK.
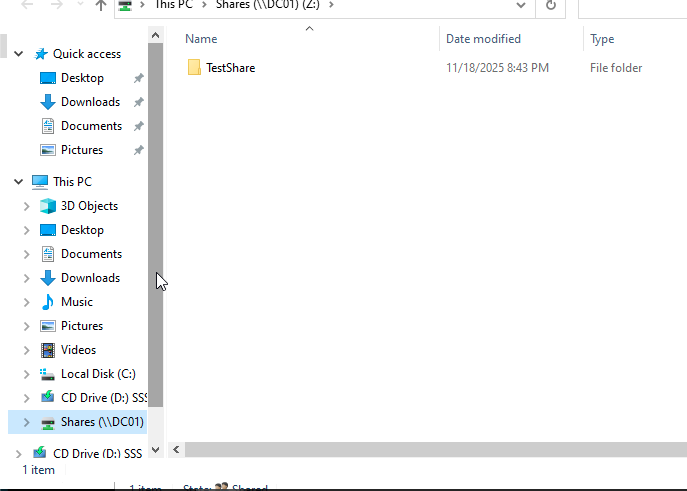
Accessing the Shared Folder from the Client
On the client, open File Explorer.
In the address bar, type \DC01\Shares and press Enter.
You should now see the shared folder hosted on the DC.
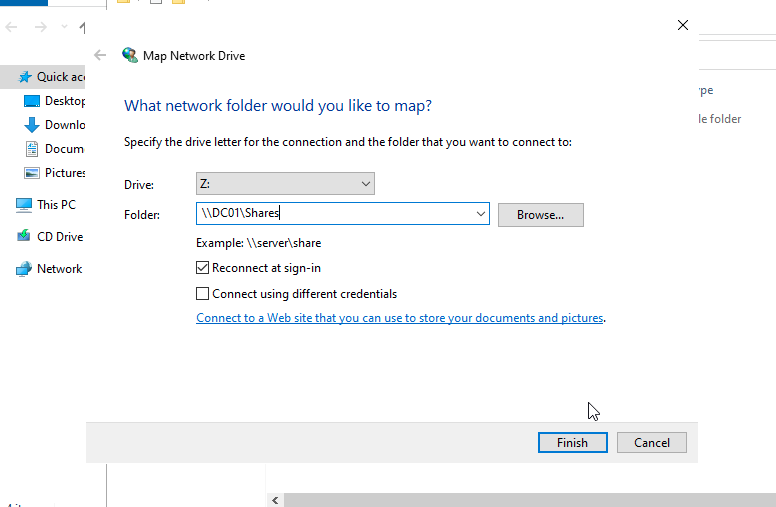
Map the Folder as a Network Drive
In File Explorer, right-click This PC > Map network drive.
Choose a drive letter (e.g., Z:).
In the folder box, type \DC01\Shares.
Check Reconnect at sign-in so it auto-connects next time.
Click Finish.
Password Policy GPO
Let’s walk through the process of enforcing secure password rules like enterprises would set up domain wide.
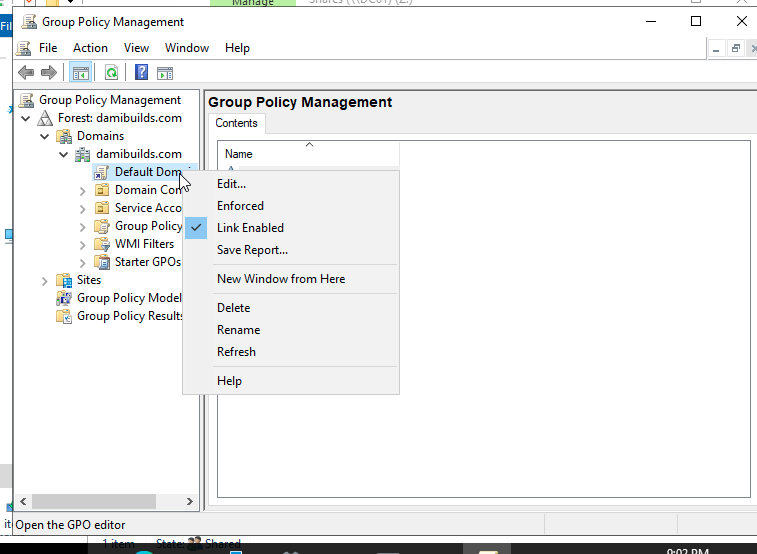
On the DC, go to Group Policy Management (gpmc.msc)
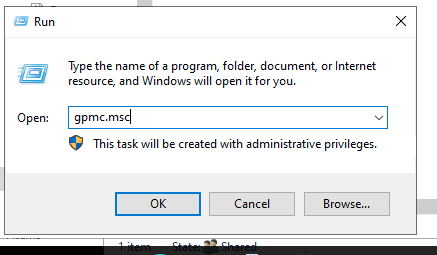
Expand Forest: damibuilds.com > Domains > damibuilds.com > locate Default Domain Policy, right click then select Edit
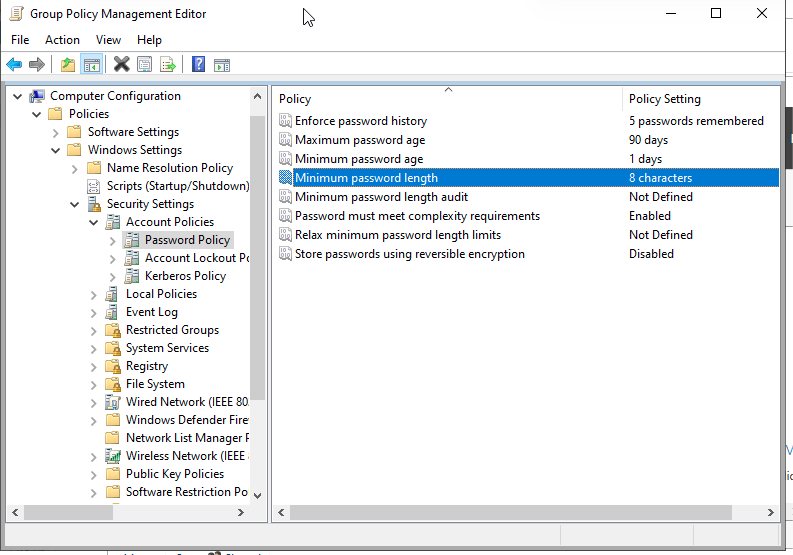
Navigate to Password Settings, in the Group Policy Management Editor, go to:
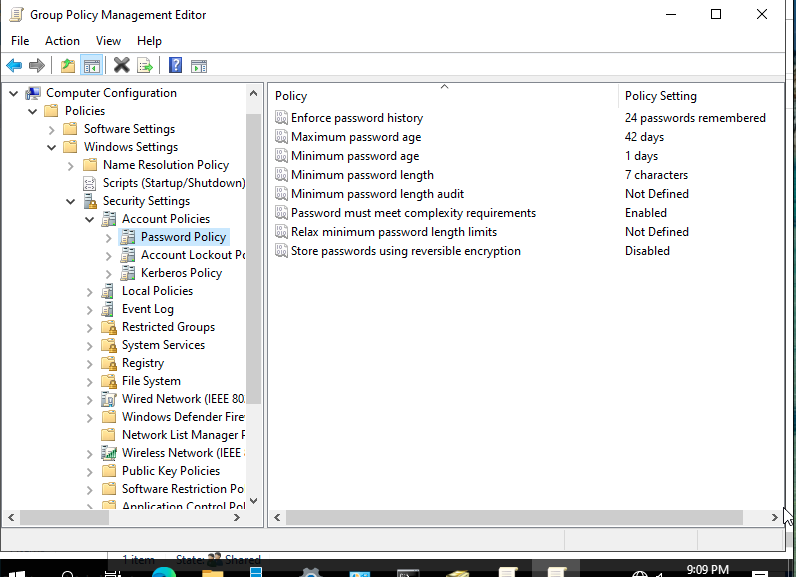
Double-click on each of the policies to change them or set them to what the organization uses. Here, I configured the following settings:
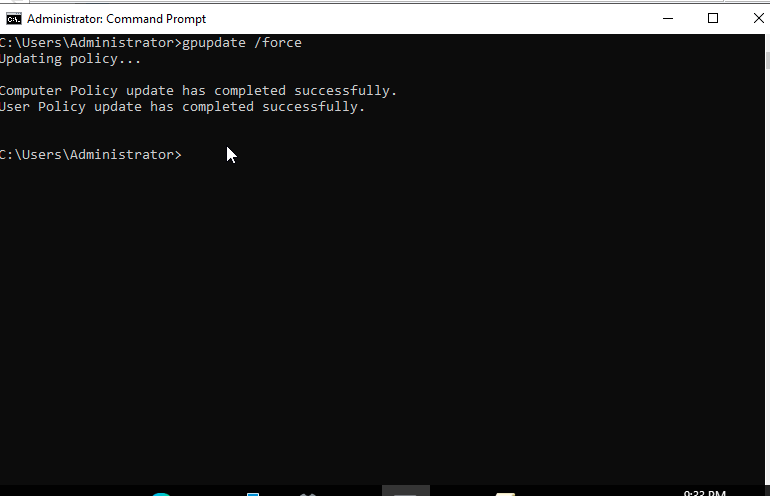
Apply and refresh policy in the command prompt with this: gpupdate /force, and the policy will be implemented domain wide.
We can also standardize user desktop background company wide, maybe it is cybersecurity month and we want to spread awareness company wide, we can set a desktop background showing that on everybody’s computer. Here’s how:
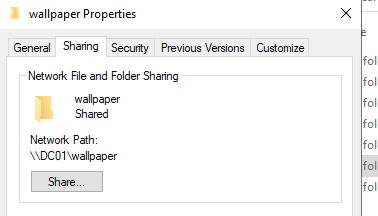
On the DC, create a folder C:\wallpaper, place the jpg, png, or whatever image file it is in the newly created folder. Right click the folder > Properties > Sharing Tab > Advanced Sharing > Share this folder. Share name: wallpaper, Permissions: Everyone > Read
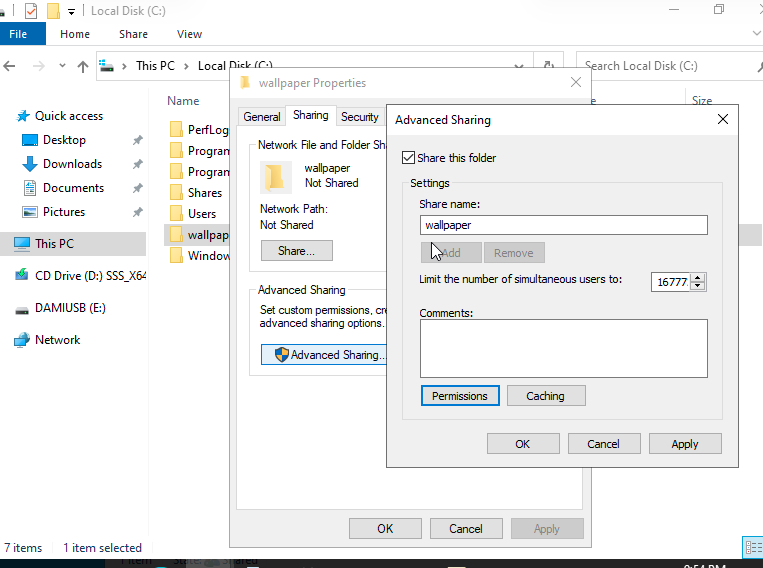
A new shared path should be generated:
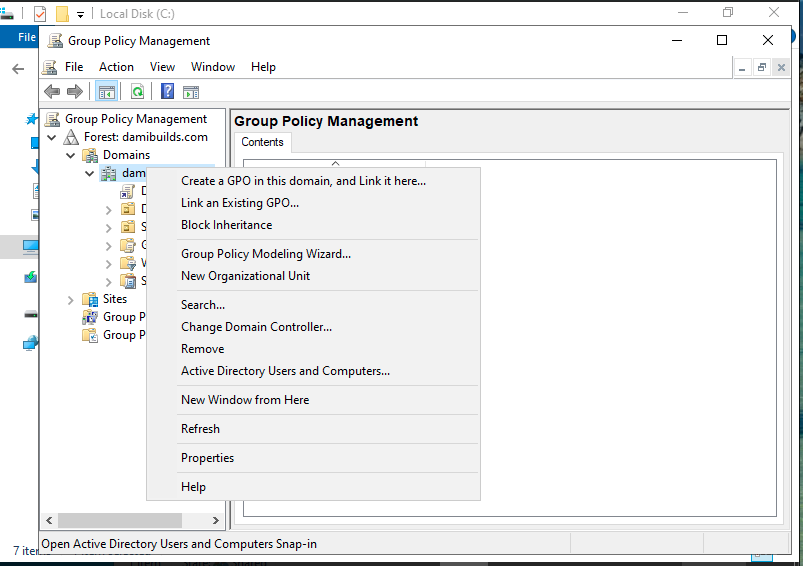
Now, create a new GPO: in the group management, right click the domain (damibuilds.com) > “Create a GPO in this domain, and Link it here” Give it a name: Set Desktop Wallpaper
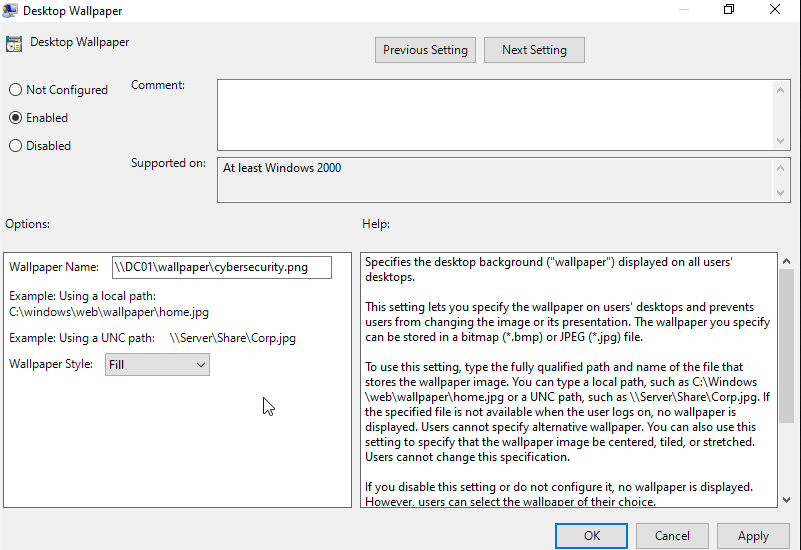
Right click on “Set Desktop Wallpaper”, select Edit and configure the policy like this:
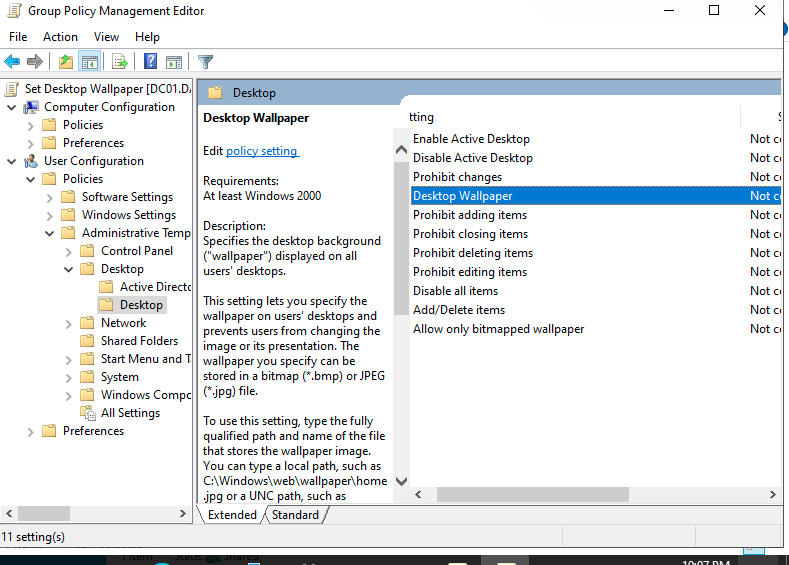
Double click on Desktop Wallpaper, and set:
Apply and set in the CMD: gpupdate /force
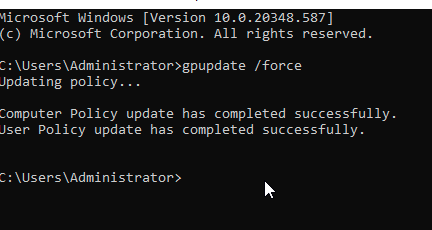
Now, lets test on the client machine. Login with the domain user damibuilds\labuser, then run gpupdate /force on the client also
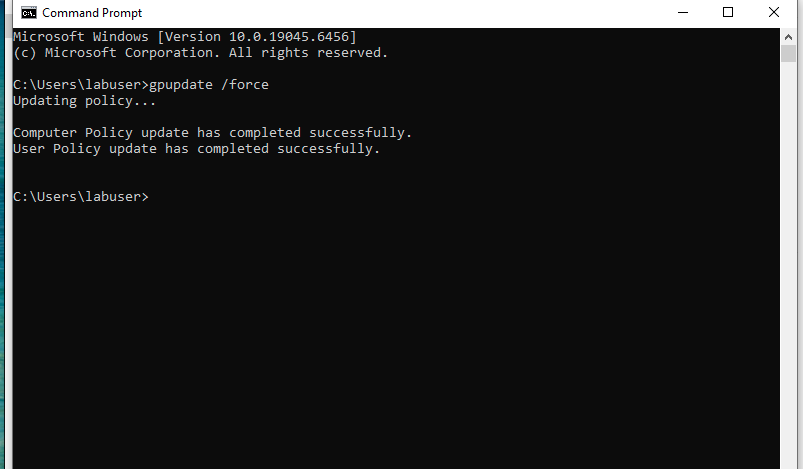 then log off and back in. The wallpaper should automatically update now, and we are done!
then log off and back in. The wallpaper should automatically update now, and we are done!